“This tiny disc of a computer is designed to defeat an Evil Maid through some very clever engineering on top of encryption tools we already use.”
We all have precious information, and we all need to store it somewhere. What happens when you’re not around your computer? For system administrators, physicians, lawyers, and journalists, protecting information is critically important. Sometimes it is even a life or death matter. And yet, when it comes to the computing hardware we all use everyday, most of us don’t even take the simple precautions that we use to protect our money. ORWL was created to bridge this gap and bring hardened physical security to personal computing.


Among information security professionals, it’s a truism that once somebody has physical access to your computer, it’s game over. Software exploits to steal data take a lot of time, money, and/or skill to pull off, and are only fleetingly effective before the vulnerability is patched. On the other hand, there are many fast, cheap, and easy ways to steal data once an adversary has physical access to your computer. The internals of a desktop or laptop computer are easily accessed and tapped for information, not to mention the myriad ways computer peripherals can hide malicious eavesdropping devices or otherwise be corrupted to work against you. This is where ORWL comes in.
ORWL was designed specifically to prevent undetected tampering with any of its electrical components, including the entire motherboard and storage drive. When tampering is detected, ORWL immediately and irrevocably erases all your data, even if it is unplugged at the time.
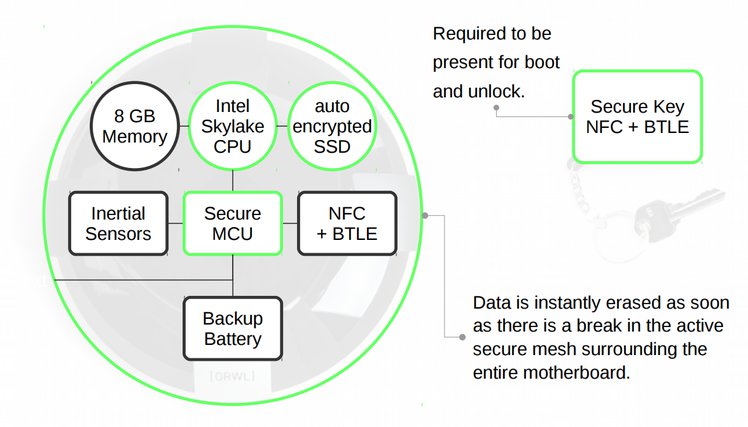
A battery-backed secure microcontroller (MAX32550 DeepCover Secure Cortex-M3) is integrated into the motherboard. It verifies the integrity of all firmware prior to boot, controls the power to rest of the Intel platform that runs the operating system, interfaces directly to an OLED display and NFC and BLE gateway for communicating with the secure key fob, and constantly monitors a dedicated inertial measurement unit, the active mesh (see below), the internal temperature, and input power voltage for any tampering. The battery itself is projected to last about six months without being connected to power.
This chip was chosen because it is powerful (108 MHz Cortex M3) and offers the highest level of security, with features that you simply cannot reproduce with general purpose microcontrollers. These features include: side channel scan protection, flip-flop based key storage, encrypted SNVRAM, glitching protection, crypto acceleration, die shield with dynamic fault detection, temperature monitoring, integrated real-time clock, true random number generation, and dedicated tamper-sensor mesh monitoring.
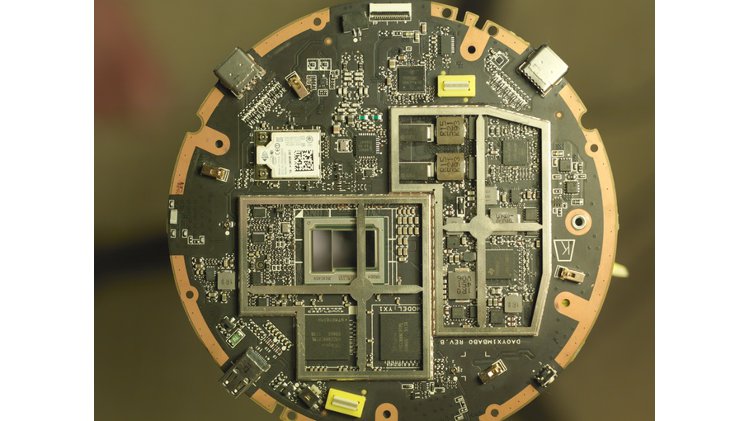
ORWL’s solid state drive (Intel SSD 540s Series) natively supports full drive encryption. The drive’s cryptographic key is generated and stored inside the secure microcontroller. The secure controller provides this key to the SSD only after verifying the integrity of the system. Upon any tampering, the secure microcontroller instantly erases the encryption key, causing all data on the SSD to be irrevocably lost.
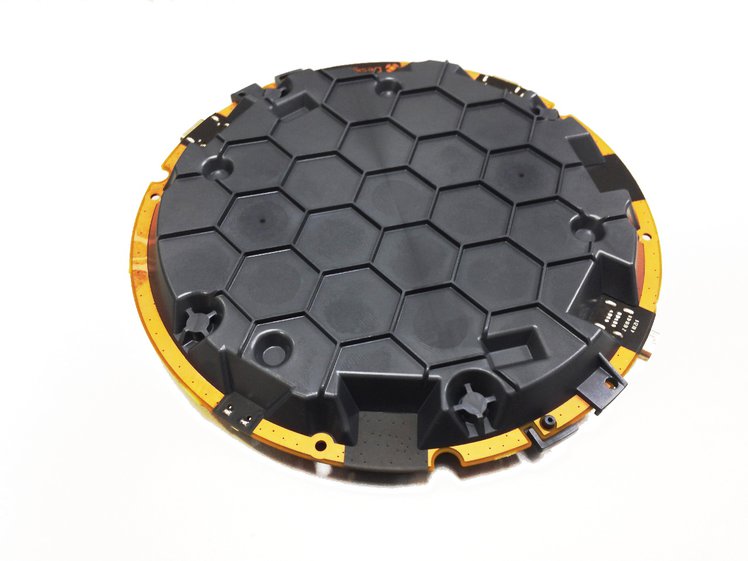
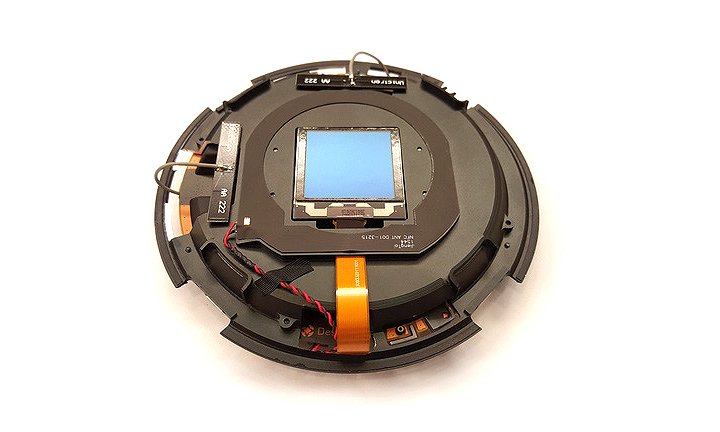
The entire ORWL system is encased in an active clamshell mesh formed by laser direct structuring (LDS), a technique for creating a resin material with finely printed circuitry designed to shatter when drilled. This mesh prevents access to any hardware component. LDS is a tamper-proofing technology used for many high security applications in banking, aerospace, defense – including hardware security modules (HSMs), security tokens, automated teller machines (ATMs), telecom crypto-key protection, defense electronics, and medical devices.
Opening the clamshell will relieve pressure switches, which will cause the secure microcontroller to delete the SSD’s encryption key. The secure microcontroller constantly monitors the mesh by sending random data through it. Drilling or cutting the LDS clamshell breaks the continuity of the printed circuit, again resulting in the deletion of the encryption key. The traces of the printed circuit are microns thick, have a nominal width of 0.3 mm, and a nominal spacing of 0.5 mm.
You can always carefully open the clamshell yourself if you want to know what’s inside, but not without destroying the encryption key. After closing it, you will have to generate a new SSD encryption key and reinstall the entire system.
Each ORWL comes with a key fob that uses the same authentication technology as smart-cards, with an added ability to detect proximity. After the initial pairing of the key fob with the ORWL to generate a shared secret, the key fob’s near field communication (NFC) is used to authenticate the user, at which point the key fob’s uses Bluetooth (BLE) to monitor whether or not the user is within range. Once a user goes out of range, ORWL will lock, requiring the key fob’s NFC authentication to unlock.

ORWL has an onboard OLED display for indicating its state: powered down, locked, and unlocked. The OLED display is entirely controlled by the secure microcontroller and is inaccessible from the operating system.
Much more detailed information about ORWL, its subsystems and components, and the design decisions that went into them can be found on our ever evolving wiki.
We are actively pursuing getting ORWL certified as a cryptographic module under a US National Institute of Standards and Technology (NIST) Federal Information Processing Standard known as FIPS 140-2. This is the standard under which the US government, financial institutions, health care providers, and other regulated industries store and process sensitive data.
The FIPS 140-2 specification, defines four levels of certification, with level four being the most stringent:
Security Level 4 provides the highest level of security defined in this standard. At this security level, the physical security mechanisms provide a complete envelope of protection around the cryptographic module with the intent of detecting and responding to all unauthorized attempts at physical access. Penetration of the cryptographic module enclosure from any direction has a very high probability of being detected, resulting in the immediate zeroization of all plaintext CSPs. Security Level 4 cryptographic modules are useful for operation in physically unprotected environments.
Security Level 4 also protects a cryptographic module against a security compromise due to environmental conditions or fluctuations outside of the module’s normal operating ranges for voltage and temperature. Intentional excursions beyond the normal operating ranges may be used by an attacker to thwart a cryptographic module’s defenses. A cryptographic module is required to either include special environmental protection features designed to detect fluctuations and zeroize CSPs, or to undergo rigorous environmental failure testing to provide a reasonable assurance that the module will not be affected by fluctuations outside of the normal operating range in a manner that can compromise the security of the module.
We are working toward and believe we have a very good chance of achieving FIPS 140-2 Security Level 4 certification, which would make ORWL the first personal computer to be so certified.
Complying with the certification requirements of FIPS 140-2 Security Level 4 is a complex, often lengthy process that takes highly specialized knowledge. To audit our work and guide us toward certification, we have engaged Penumbra Security, a NIST-accredited information security firm specializing in FIPS 140-2 compliance testing. Penumbra’s initial audit of ORWL has already resulted in several improvements to the design. We intend to continue working with Penumbra throughout the certification process.

Security through obscurity is not security. We want the inner workings of ORWL to be transparent, so that it can receive the inspection necessary to build real trust. You shouldn’t need to take our word on how secure ORWL really is – you should be able to see for yourself.
ORWL is a complex product, with many pieces that could possibly be open sourced. As such, we are still working through exactly which licenses will be used and how best to make available all the information. We will make updates on this page in the coming days. Here’s what we know and are committed to at this point:
Sign up for reminder emails above and watch this space for updates. We anticipate having all licenses sorted out very soon.

ORWL is available with a glass enclosure (as shown in most of the images on this page), a plastic enclosure that is roughly the same dimensions as the glass enclosure, and bare without any enclosure.

ORWL with a plastic enclosure
The glass enclosure is heat formed, then machined and polished. The glass is 2.8 mm thick and chemically hardened, so that it will not accidentally break when dropped: the target drop resilience is 0.6 meter onto marble.
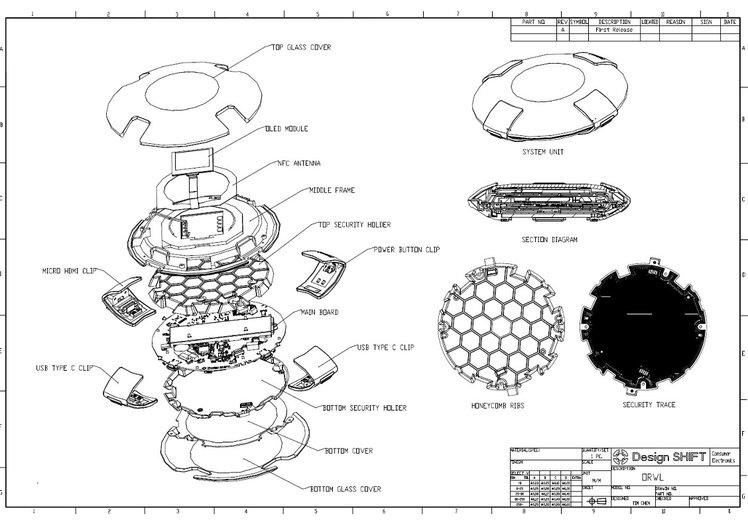
ORWL is designed to be easily (though carefully) disassembled and reassembled. Disassembling ORWL will erase the encryption key, rendering encrypted user data inaccessible. You will have to regenerate an SSD key and install a new operating system. That said, and because you should have backups of your data anyway, disassembly is possible provided you are careful. We cannot assume liability if you were to break the shield or any other part while disassembling. For ease of assembly, the screws are all identical: black, same length, with a Torx T8 head.
Up to three bare ORWLs without any enclosures can be mounted to a specially made 1U rackmount chassis. ORWL’s key fob behavior can be configured to accommodate server use.

ORWL rackmount chassis


This project is about having a standard, physically secure computer that anyone can use – as open as we can make it. All these concepts are important, and they mean that x86 and flawless out-of-the-box Windows support are not optional. There are reasons everyone is using x86, even in the security community and in governmental agencies around the world: compatibility, performance, and security. Make no mistake, some of us own Yeeloongs, and others are veterans of the silicon industry. We would love to ship a completely free and usable desktop processor, but we know very well that there is no alternative. Some people seem to think that switching to AMD can solve problems related Intel’s Management Engine (ME), microcode, or SMM. It doesn’t, as there are equivalents of these technologies in all recent x86 processors.
We will not ship machines with Boot Guard “Verified Boot” activated. While we do implement a firmware verification mechanism on the microcontroller, you can choose to provision your own signing keys or not to use it at all.

The following are some of the specific attacks ORWL protects against.
Attacks: Cold boot attacks consist of removing the DRAM or power-cycling the machine in order to read the memory content. The DRAM is often chilled to slow down the loss of information that occurs when the cells are no longer refreshed.
Mitigations: The DRAM is soldered, and protected by the active clamshell mesh. Cooling down the secure microcontroller will trigger a tamper event, erasure of the encryption key, and system power down. Encryption keys are only stored in the main memory by the UEFI for an extremely short time before they are passed to the SED, and are securely memset’ed long before the OS is booted. When the machine is put in sleep mode while the user is away, the key is not stored in the main memory nor in the SED controller memory. To prevent other kinds of attacks on the memory content, the entire RAM is wiped before the OS is booted.
Attacks: UEFI BIOS, SMM attacks, and all sorts of platform vulnerabilities allow an attacker to run very privileged code that is both invisible to the OS and capable of achieving persistence by modifying the SPI flash. The UEFI image can also be modified by physical access to the component.
Mitigations: We are in direct contact with the UEFI vendor and will work on patching public vulnerabilities. In the event that an attacker is able to exploit an SMM, UEFI, or platform vulnerability, there is no vector for persistence. The SPI flash Write Protection is controlled by the secure microcontroller, and the update process can be tied to a specific keyfob or pin. The SPI flash content is also verified at every boot, before the Intel subsystem even receives power. Finally the external verification process allows you to easily read the flash and verify it.
Attacks: External DMA attacks over PCIe or Firewire can allow an attacker to read the memory content while the machine is running.
Mitigations: We do not expose DMA-capable ports externally. For internal ports, the SED we selected is not PCIe capable. The Intel processor also supports VT-d, allowing you to block this class of attacks from software.
Attacks: The device is intercepted during shipping, modified, then forwarded to its destination.
Mitigations: The system PIN will be shipped under separate cover, as is done with credit card or debit card PINs. If the device is opened for tampering prior to arrival, the root of trust (SSD encryption key) is deleted. Replacing this requires a paired keyfob and the PIN. The result is that the owner will not be able to successfully boot the device if it’s been tampered with in this way. Because you have visibility into firmware, most software implants are very risky to use for your attackers. The hardware is protected by the shield, and the OLED screen that is the only exposed component is protected by a dedicated mesh. The screen’s flexible flat cable has a mesh on both sides, and is just as long as required. The space between the glass enclosure and the shield is also minimized.
We’ve manufactured and tested several design and engineering iterations of ORWL prototypes. We are now ready for the first production run. If this campaign successfully reaches its funding goal, we will start production and wrap up what BIOS development remains to make ORWL feature complete.
We (Design Shift) have years of experience in product design, engineering, and manufacturing, with full-time staff in both our Menlo Park and Taipei offices. Our manufacturing partner for ORWL is Taiwan-based Quanta Computer, one of the world’s largest computer manufacturers. We are also working directly with many of our suppliers, such as Intel, STMicroelectronics, and Maxim.

Our team and partners have copious experience mitigating the supply chain risks inherent in manufacturing any nontrivial product and have taken the same care with ORWL. On our website, you can see some of the products we’ve previously designed and brought to market, such as the X1 Digital Camera, Clover point-of-sale system, and the Robin by Nextbit smartphone.
The biggest risk in bringing ORWL to life is not whether it can be done, but how long it will take. We’ve laid out a conservative delivery schedule, but of course there may be surprises along the way that change that schedule. The biggest risk in this regard is the remaining BIOS development. While we have already made significant strides in the BIOS, there are some features that are not yet complete. In preparation for finishing the BIOS, we are currently in talks with a professional BIOS development team.
Regardless of how the production schedule evolves over time, we commit to publicly and transparently communicating ORWL’s production status together with updated estimates of the delivery schedule.