In today’s API-driven world, security is a must if you want your API to function as intended. In the past few years, API security has been an increasing concern for many companies and developers alike. If you don’t perform API security testing, you’re making it easier for hackers to exploit your application. The goal of this guide is to help you understand what API Security Testing entails.
API security testing is an approach used by software developers and API testers to identify and mitigate API vulnerabilities. You have to test APIs or applications that communicate with an API, such as mobile apps and websites. Security testing of APIs can help to identify vulnerabilities in your API so you know where the biggest problems are. It is recommended that API Security Testing be done at least once a year or after any code change. But ideally, it should be part of every test cycle. 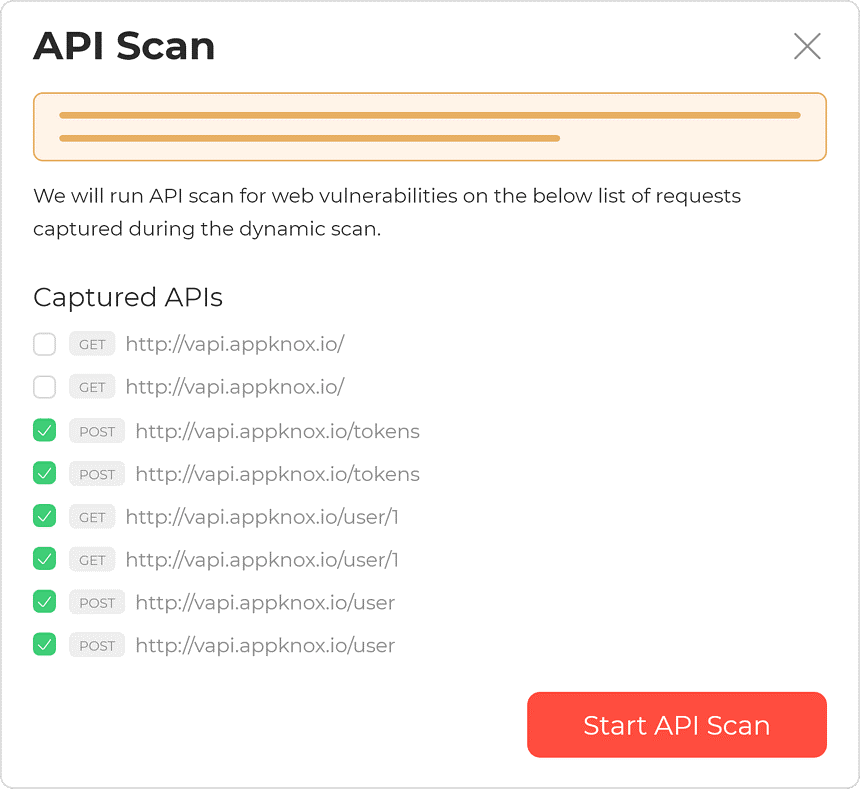
Source: Appknox
API security testing is important because developers can address it before they become API exploits. It will help you to ensure your API is working as intended. You don’t want it to open up any unnecessary API leaks or API breaches for attackers to exploit. Such vulnerabilities can allow attackers to spoof data, tamper with requests and responses or otherwise gain unauthorized access to your API.
There are several different kinds of vulnerabilities that API testing should include. The following list provides an overview of some common ones:
What to do if a user sends a malformed request as part of an API call? You need to make sure your API can handle invalid input and doesn’t allow for API vulnerabilities. Input fuzzing involves passing malformed data through the API. Hackers do this to find areas where it may cause application instability or crashes. It’s also useful for finding unhandled exceptions which can lead to potential injection attacks if left unchecked. Checkout the detailed guide on 11 Tips to Own SaaS Security For example, let’s say your company offered a function on their website so users could retrieve API keys. If you passed in the API key as the username, then any company that didn’t check for this could allow anyone to access the API Keys of their users without permission or notification.
What if a user sends malicious code as part of an API call? You need to ensure that you don’t have any API security flaws or fail to validate certain types of data in order to prevent API exploits such as SQL injection attacks. API security testing should include API Injection attacks because they can expose sensitive information if left unchecked. API Injections occur when a user sends an API call to the application but with malicious code. The webserver or other backend processes/services will execute this, allowing hackers to steal important data from databases and more.
What happens if a user sends an API call using an unauthorized method? Unhandled methods are API calls which the developers did not intend for their API to handle. They can be useful in identifying potential logic flaws that could lead to other security issues. This includes any kind of requests made via GET/POST/PUT/DELETE etc.. It helps you find areas where a developer may have forgotten about a particular method they should have been handling (e.g.: getting all orders from an e-commerce site).
What if a user sends API requests with altered parameters? You need to ensure that you validate all API request parameters. This will help you prevent unauthorized changes from being made and any attempts at API exploits such as cross-site request forgery attacks. For every request sent through an API, there are usually one or more parameters used (e.g.: name=John&email=john@gmail.com). Testing for parameter tampering helps you identify malicious such as login CSRF attacks.
API testing should include API misconfiguration because it can leave API vulnerabilities and cause a range of security issues. Misconfigurations occur when the API is not configured to handle unauthorized or unknown requests that would otherwise be blocked by an app firewall, IDS/IPS, or other similar tools which allow only authorized traffic through the network perimeter.
API security testing should include API brute force attacks. It allows hackers to gain access to your entire user database by trying various usernames and passwords. Brute force API occurs when a malicious party uses automated tools such as Crawljax, Burp intruder, or other similar bots which can test brute force login against an API in order to gain access to API keys for your entire user database.
In the end, API security testing is a necessary step to take in order to ensure that your app or website isn’t vulnerable. You may get an overview of everything you need from this article. Now it’s time for you to start looking into finding an API tester who can help with any vulnerabilities. Good luck!