WHO WE ARE:
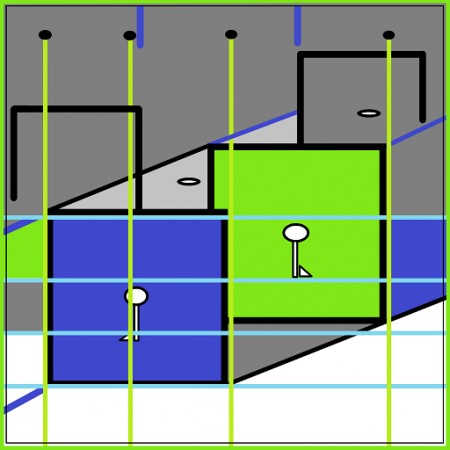
On the 10th of August 2015 here on we represent a computer firm (PC-Integral, Inc) in Twin cities, MN. We had a very humble beginning. We have been in operation since 2006. We have grown into design and development of security products and tools regardless of insurmountable difficulties. Most of our work is consulting with fortune 500 organizations. Currently, we have invented an encryption system which we have used to build a vanguard prototype called LokDon.
WHAT WE OFFER:
There has never been a time when humans needed privacy than now. We have a better way of performing encryption with a new base technology called skcjju256. This technology evolved over 15 years of development. After extensive research and development we are confident to share this with you. This technology is based on the movement of a knight on a chess board. We strictly mean the legal movement of a knight on a chess board of m * n dimension. Why did we decide to approach the problem from this angle? We noted that whenever two people are playing the game of chess one will ultimately emerge as the victor either by rendering the king immovable or by capturing more pieces, which means more points. So from these vantage point we can tell that we are on the right track at least. It wasn’t until 2010 which was exactly 10 years starting from 2000 when the idea was first conceived that I realized the strength in the movement of the knight.
It is a well known fact that a knight can move continuously from a square (white or black) while touching all other squares on the chess board at least once absent back tracking and without landing on the original starting point. This functional practice is what they call open knight’ tour. I figured that if there is way to use this to hide components of written language then it is possible to hide information with the it. So this moment when successfully completed without any hiccups presents sets of numbers which forms families (same starting positions); yet different from each other by a very significant margin. The combination found in these families are quite infinite thus, they can serve as perfect master keys in the age we live in.
Finally, I solved the problem completely in 2013 by harnessing these numbers. I sought patent to the work in 2012. I also published my work on www.skcjju256.com while withholding other necessary and intellectual details from all prying eyes. In 2014 we launched two prototypes; skcjju256 for windows and LokDon ver 1.0 for Android. The whole idea is for you to get a feel of what we are doing and to see for yourself how it works. In the research, I noticed that the process in the AES algorithm is analogous to Rubik’ Cube. I also noticed that the scope constraint in AES makes it possible the use of S-Box. All these simply means that the mechanism is slower, data consuming and it is not easily implemented in hardware. We found out that the base technology extends AES both in complexity and compression. It has 8 times AES’ capacity and this simply means that we won’t have to worry about nothing when quantum computing arrives. Today, authorities in cryptography agree on all fronts that encryption is the best way to protect data integrity. The only question left now should be this one. Is it possible that we have found a way to extend AES which is the state of the art in block cipher cryptography? To answer that question let us show you the advantages of our base technology and you can conclude for yourself.
The advantages of our base technology:
1} Our cryptographic surface has a way of compressing data and making it smaller than AES algorithm. The IV, Roundkeys, Subbytes and Rounds (these are scope dependent) adds to the AES ciphertext and that is by far not the case with our system. Our system will redeem appro. 40% percent of every 100% encryption done by AES in unused storage space.
2} As you can see from line 1 it will increase the speed of SSL/TLS communication protocol used in VPN technology in many private and enterprise environment.
3} It will be used in conjunction with PGP to provide a circle of trusted users.
4} It will provide capability of non-constant master keys since the keys are infinite.
5} The algorithm is not agnostic to just application or programming. It can equally be used in any field requiring security. The millions and billions of combination and permutation is the power in our generated numbers therefore we find them useful in many fields and specific technologies. Smart card for secure ID in the military, high level personnel secure ID, Network communication, Video streaming, telecommunication (video streaming) and Mobile device (cellular phone voice encryption),etc.
6} It will provide absolute visibility for security incident response as an end-point to end-point tool.
7} It will remain formidable and durable in the face of quantum computing since it is 8 times better than the state of the art.
8} From line 5 you could be assured to use it anywhere from embedded to compressing encryption technology e.g DeciBit WIFI crypto and AWS will find it very useful.
Implementing skcjju256 with LokDon:
Encryption video— https://www.youtube.com/watch?v=oIND8VN1kOw
Decryption video– https://www.youtube.com/watch?v=LoeSRiC75MA
Special case of the reason why Amazon is a big gainer (#9 advantage):
https://aws.amazon.com/s3/faqs/
AWS S3 (We assumed that these data where all encrypted)
Storage Example:
Assume you store 100GB (107,374,182,400 bytes) of standard Amazon S3 storage data in your bucket for 15 days in March, and 100TB (109,951,162,777,600 bytes) of standard Amazon S3 storage data for the final 16 days in March.
At the end of March, you would have the following usage in Byte-Hours:
Total Byte-Hour usage
= [107,374,182,400 bytes x 15 days x (24 hours / day)] + [109,951,162,777,600 bytes x 16 days x (24 hours / day)] = 42,259,901,212,262,400 Byte-Hours.
Let’s convert this to GB-Months:
42,259,901,212,262,400 Byte-Hours x (1 GB / 1,073,741,824 bytes) x (1 month / 744 hours) = 52,900 GB-Months
LokDon will give you 52,900 GB-Month – 0.35*52,900 = 34785 GB-Month
This usage volume crosses three different volume tiers. The monthly storage price is calculated below assuming the data is stored in the US Standard Region:
1 TB Tier: 1024 GB x $0.0300 = $30.72
1 TB to 50 TB Tier: 50,176 GB (49×1024) x $0.0295 = $1,480.19
50 TB to 450 TB Tier: 1,700 GB (remainder) x $0.0290 = $49.30
Total Storage Fee = $30.72 + $1,480.19 + $49.30 = $1,560.21
LokDon will give you a total of $1,560.21-($1,560.21*0.35) = $1014.1365.
You are saving exactly $546.07
Future Plans and projects:
1} First Phase:
Build a web portal for EBS integration. Modify the present application for local and other authentication methods. This will follow through iOS, Android and Windows platforms
2} Second Phase:
We will build a mobile app. for all three major platforms and web services for end-users: Cloud and social media integration across the board using effective PKI.
3} Third Phase
We will build a windows based server client version which will address security within incident response teams. This will be a major tool for SIRT in many organization and enterprises seeking secured electronic connection gateways.
Companies we will like to share technology with:
WHAT WE NEED:
} Co-founders
} Mentors
} Seed money
} Incubator program
} Web application Developers
} Programmers
} Mobile application developers
} Security architect
} Designers
} Marketing/Sales
} Legal counsel
CONCLUSION:
Our base technology is outstanding in all areas tested. We have no fear that it is here to stay. The challenge is thrown out to any disapprover to show us where modification is needed. The fact that you are reading this right now is the confidence we have that you will understand the effort we have put in to bring this knowledge to you.
In a dynamic world there is no better way to change a single thing if we can not acknowledge a better idea and make it flourish. We can test it for ourselves and become convinced: It is also our duty for us to make it a public knowledge to educate others in a better way of doing things. This we must do in order to preserve wisdom and the dignity of humanity.
We welcome criticisms new ideas and we also want to work with all suitable companies. The encryption between the internet and your computers, IoT and handheld devices will be done seamlessly regardless of the capacity. You will be able to re-gain and maintain your privacy once again with lesser foot-prints.