
Dear Investors,
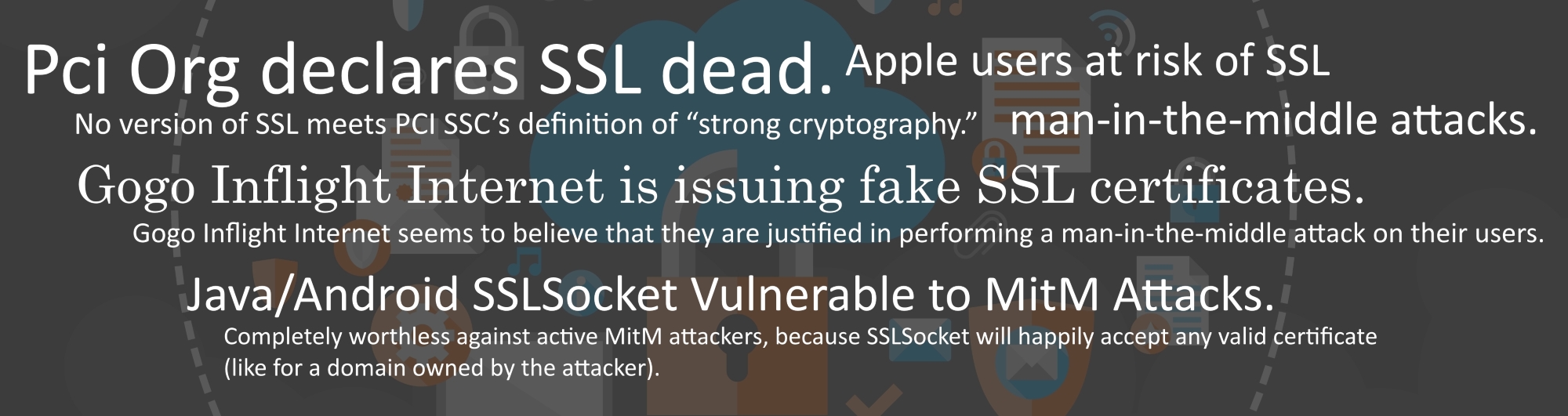
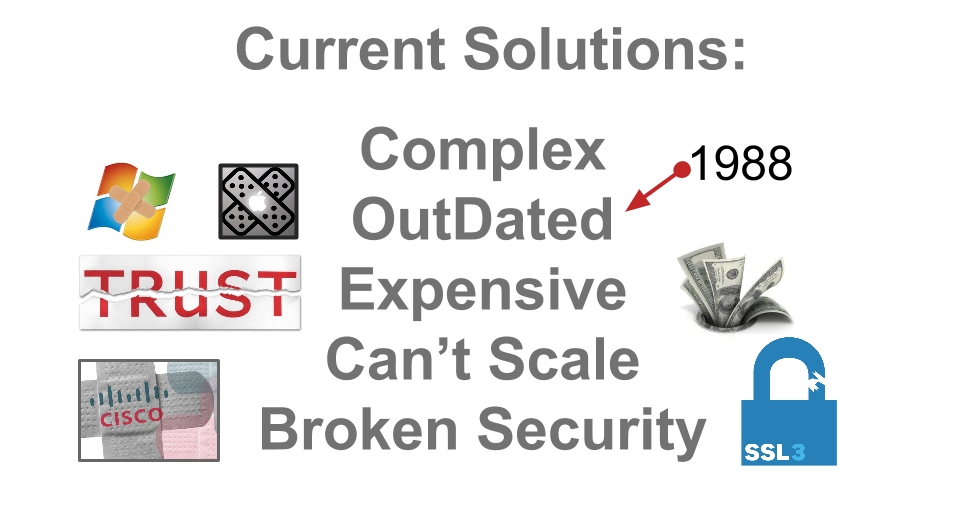
For the past 12+ months we’ve watched in complete amazement as the IT security industry continued to deny the existence of the real and escalating Internet security issues. These issues can’t be mitigated, audited, patched or managed to return security to the Internet.
So what about transport? Still going to use SSL(HTTPS)/TLS/IPSec? “Yes” what else do we have? “Look” Target, Sony and Lockheed were hacked they were using 2FA and PKI didn’t help them any – so why not up the bar make this the rock star business solution. You’ll need more than a “moat”. You will need fluid security. It might be hard to believe but we’ve found a way to deal with the transport and end points that “WORKS”…and addresses the secure connectivity ecosystem. Our approach to these challenges provides friction free integration, in other words “business as usual”, this is a big deal because business can’t afford to be offline or disrupt the user experience… http://www.e-magik.com – founders@e-magik.com
We do this because it must be done!
If we really want to fully leverage the virtual world it must become secure and private or we’ll never reach the goal of a connected world, because no one will buy into these risks regardless of the perceived benefits. Our online security and privacy are no longer nice to have they’ve become must have.
We’re becoming a traded commodity where our most personal information is traded and sold by companies’ and hacker’s, collected by government’s all of them having no interest in our well being.
It’s a matter of self preservation now and in the future!
e-Magik is a cyber security startup addressing secure connectivity, whether it’s our businesses, our phones, our homes or cars – made by Apple, MS, Intel, Google or Samsung…Mobility is no longer the point. Mobility is expected. Securing this connectivity is the point! This is why we developed “Fluid security” — eM-Connect™.
“Wrap it in SSL/TLS/IPsec if you must, But ship it with eM-Connect™”
Get involved it’s your security and privacy at risk too.

Jan. 25th 2015 – Gartner: “By 2017, 50% of network attacks will use SSL/TLS”
In fact, 50% of all network attacks will hide in SSL by 2017, according to Gartner; and today, 80% of attacks that use SSL/TLS and HTTPS go undetected until it’s too late. Why? Because they can’t detect these attacks!
The IT Security Industry is in denial – Internet security is broken – they know it – but can’t fix the tools they have – it’s a design issue with no possibility of repair! We’re sure you follow the major IT headlines like; Target, Sony and Anthem breaches. The underlying question is why and how do these breaches and exploits happen over and over again? The answer is not as complicated as you might suspect, It’s actually a simple matter of the “chain of trust”. What was envisioned in 1988 to provide secure network communication is no longer suitable for today’s Internet of Everything.

Industries and people are using an ever increasing number of web-connected devices, from smartphones, tablets and laptops to home appliances, medical devices and industrial controls. But more than 80% of these connected devices are not secure because “Industry Standard” security methods are broken!

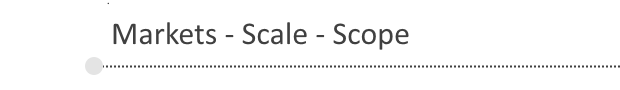
Compliance And Security Slow Cloud Adoption Joseph Granneman, CEO & Principal Consultant at Illumination.io, characterizes the challenge, “Concerns about regulatory compliance and data security have put the brakes on cloud adoption at many firms”.
PCI DSS The impacting change is related to several vulnerabilities in the SSL protocol. Troy Leach, Chief Technology Officer at SSC, “No version of SSL meets PCI SSC’s definition of strong cryptography, and updates to these standards are needed to address this issue”.
IoT has struggled with security threats and breaches. According to Samsung Vice President Dr. Alan Messer, “privacy is a big problem,” and security could halt connected innovation before it is able to hit the mainstream.
 A recent study by the Center for Strategic and International Studies estimated that the annual cost of cybercrime to the global economy ranges from $375 billion to as much as $575 billion…
A recent study by the Center for Strategic and International Studies estimated that the annual cost of cybercrime to the global economy ranges from $375 billion to as much as $575 billion…
If that figure seems high, it doesn’t even approach the estimates of losses that can result from theft of trade secrets and intellectual property.
Using the World Bank’s annual global GDP estimate of $74.9 trillion in 2013, loss of trade secrets may range from $749 billion to as high as $2.2 trillion annually…
The world needs a real secure connectivity solution NOW – Not Patches and fixes to a flawed and broken “Industry Standard”!

 The entire eM-Connect™ ecosystem is designed and developed with you in mind. “User Experience” really matters! End users want what they know and know what they want. Sysadmins face layers upon layers of complex systems and tasks. Service provider margins are tight, complexity is really expensive. Developers need a flexible, secure connectivity “snap in” to simplify development. We’ve made secure connectivity accessible and simple, by focusing on the entire ecosystem’s User Experience.
The entire eM-Connect™ ecosystem is designed and developed with you in mind. “User Experience” really matters! End users want what they know and know what they want. Sysadmins face layers upon layers of complex systems and tasks. Service provider margins are tight, complexity is really expensive. Developers need a flexible, secure connectivity “snap in” to simplify development. We’ve made secure connectivity accessible and simple, by focusing on the entire ecosystem’s User Experience.
The eM-Connect™ platform addresses modern “Web Scale” systematic approaches to provide scalable, distributed, secure, and reliable connectivity services. Our “fluid security” methods let eM-Connect™ scale from SME to Google levels because of design.



Your Internet Security matters!

Simple – Complexity = Expense + Risk.
Scalable – Up and Out

User-Friendly – The Ecosystem.

Fluid Connectivity – Like the Internet.

Engineered Magik’s vision is to return security and privacy to the internet, thus enabling new products to become secure and private, and opening the door for new innovative applications that otherwise could not be deployed or developed due to the cost and complexity of addressing security concerns. The key to this is a disruptive technology that must deliver non disruptive consumer adoption to ensure rapid and sustained growth. Engineered Magik provides unparalleled simplicity in solving these challenges, allowing users, service providers and developers to focus on doing what they do best.
 People have always thought of security as something complex, esoteric, inflexible and expensive. Because of that, security has always been treated as an add-on technology, not as a design requirement.
People have always thought of security as something complex, esoteric, inflexible and expensive. Because of that, security has always been treated as an add-on technology, not as a design requirement.
Engineered Magik is a security ecosystem that focuses on the entire network. We’ve created a secure private connectivity environment that benefits users, service providers and developers alike. Our simple “Snap-In” solution keeps security affordable and flexible.
The eM-Connect™ Snap-In solution works in two easy steps.
 The core connector is a free download on the Internet.
The core connector is a free download on the Internet.
 Once deployed, any participating service provider can enable services on any of your devices.
Once deployed, any participating service provider can enable services on any of your devices.
eM-Connect™ is deployed to your device, operates silently, nothing to configure no user endpoint settings. Once logged in, it’s simply transparent. You can’t even see that it’s running, but you’ll know that it’s working. We’ve reversed the connectivity configuration model. This change puts all aspects of; security, connectivity, applications, resources, services and user experience, where it should be, in the hands of the IT security professionals.

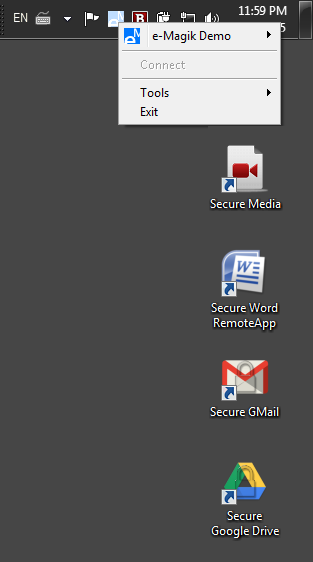
Engineered Magik has had great traction so far and we’re thinking ahead to the future.
Traction
 Hosted Beta1 stage completed
Hosted Beta1 stage completed
 Overwhelming response for 3 proof of concept releases
Overwhelming response for 3 proof of concept releases

Patents filed
 Incorporated November 2013
Incorporated November 2013
 Attracted interest from Oil & Gas – Telecom – Healthcare
Attracted interest from Oil & Gas – Telecom – Healthcare
Beta launch – March 1st 2015 
 Beta customers in Healthcare – Telecom – Oil & Gas ♢ Q1 2015
Beta customers in Healthcare – Telecom – Oil & Gas ♢ Q1 2015
Exit Strategy
 We are pursuing Secure connectivity because most big companies aren’t innovative enough, in the medium term we see the entire industry benefiting from our initiative…
We are pursuing Secure connectivity because most big companies aren’t innovative enough, in the medium term we see the entire industry benefiting from our initiative…
 Alternative initial public offering in 3-5 years
Alternative initial public offering in 3-5 years
 Craig Damon, CEO
Craig Damon, CEO
With over 30 years on the leading edge of software development and business management, Craig’s vision and attention to detail, quality and usability are a driving force behind our strategic technology development. He is co-inventor of patented software methods and cofounded Giritech with partner Jimi Jorgensen.
 Jimi Jorgensen, CTO
Jimi Jorgensen, CTO
Our resident coding wizard Jimi is an expert in software development and a specialist in the fields of internet security, software and IT architecture, system operations and applied cryptography. He is co-inventor of patented software methods and cofounded Giritech, which has successfully merged with Excitor A/S.